
I recently watched an excellent TED Talk by Julia Galef, that should be a “must read” for every HR professional who is tasked with the responsibility of conducting employee investigations. As explained below, applying the points made by Ms. Galef can improve your company’s response to allegations of discrimination or workplace misconduct, as well
 A recent decision of the National Labor Relations Board provides employers with a reason to carefully evaluate disciplining employees who make negative comments about their company’s products. Specifically,
A recent decision of the National Labor Relations Board provides employers with a reason to carefully evaluate disciplining employees who make negative comments about their company’s products. Specifically,  Investigating employee misconduct is, unfortunately, a common occurrence companies and their HR professionals experience. But if the investigation is not properly handled, it could expose the employer to liability, including being sued for defamation.
Investigating employee misconduct is, unfortunately, a common occurrence companies and their HR professionals experience. But if the investigation is not properly handled, it could expose the employer to liability, including being sued for defamation. Today is April 20, 2015. However, for certain individuals who partake in smoking a plant in the cannabis genus, it is also “420.” The use of “420” has
Today is April 20, 2015. However, for certain individuals who partake in smoking a plant in the cannabis genus, it is also “420.” The use of “420” has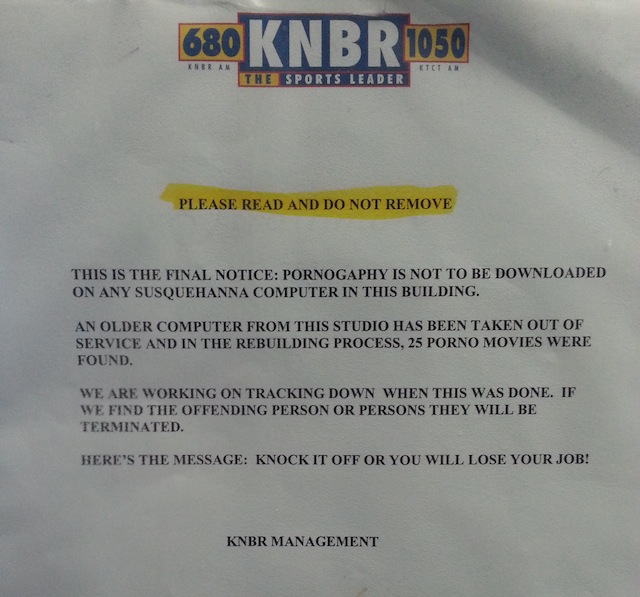 One employment law topic that never seems to go away is pornography in the workplace.
One employment law topic that never seems to go away is pornography in the workplace.
 A well written article by
A well written article by  In the fall of 2008, 63% of Michigan residents voted in favor of legalizing medical marihuana. Despite this majority, Michigan legislators continue to whittle away at that law.
In the fall of 2008, 63% of Michigan residents voted in favor of legalizing medical marihuana. Despite this majority, Michigan legislators continue to whittle away at that law. The Food and Drug Administration (FDA) was sued by six on-staff doctors and scientists after discovering the FDA accessed their personal email accounts (Gmail).
The Food and Drug Administration (FDA) was sued by six on-staff doctors and scientists after discovering the FDA accessed their personal email accounts (Gmail).