 Last week I had the opportunity to present at the 2011 Thomas M. Cooley Law Review Symposium’s Who’s Mining Your Business: Privacy Infringement and Profits. The Law Review members, spearheaded by Dayana Echeverry, put together a phenomenal program. It was a great opportunity to share the stage with an incredible panel of Internet privacy and data mining thought leaders. Specifically, Dick De Veaux and Chris Clifton and Andreas Weigend. Also, Professor Derek Witte did a great job (as usual) moderating the event.
Last week I had the opportunity to present at the 2011 Thomas M. Cooley Law Review Symposium’s Who’s Mining Your Business: Privacy Infringement and Profits. The Law Review members, spearheaded by Dayana Echeverry, put together a phenomenal program. It was a great opportunity to share the stage with an incredible panel of Internet privacy and data mining thought leaders. Specifically, Dick De Veaux and Chris Clifton and Andreas Weigend. Also, Professor Derek Witte did a great job (as usual) moderating the event.
Here is a copy of my presentation, which focused on Information Protection and Privacy Law for businesses (PDF).
While the overall focus of the seminar was on consumer data mining and the applicable regulatory and legal landscape, here are a few important points relevant to employers and employees.
Michigan Data Breach Notification Statute
Michigan, like most states, has a data security breach notification law. This law imposes certain obligations on businesses if there is breach of “personal identifying information” (Personal Information”). Personal Information is statutorily defined, but it includes information commonly collected by businesses in the ordinary course of operations, such as name, contact information, social security number, place of employment, mother’s maiden name, a person’s account password, or credit card number.
Under Michigan’s data breach law, one trigger for notifying consumers of a data breach is the access and acquisition by an unauthorized person of unencrypted or unredacted computerized data or of encrypted data if there was also unauthorized access to the encryption key. MCL 445.72. Failing to comply with the notification provisions of Michigan Data Breach statute is $250 for each failure to provide notice, with cumulative liability not to exceed $750,000. MCL 445.72(12).
In terms of national numbers, the nonprofit Identify Theft Resource Center identified over 360 data breaches that have occurred through September 2011. These breaches involve cumulatively over 13 million records.
Employees are often the Cause of Most Data Breaches
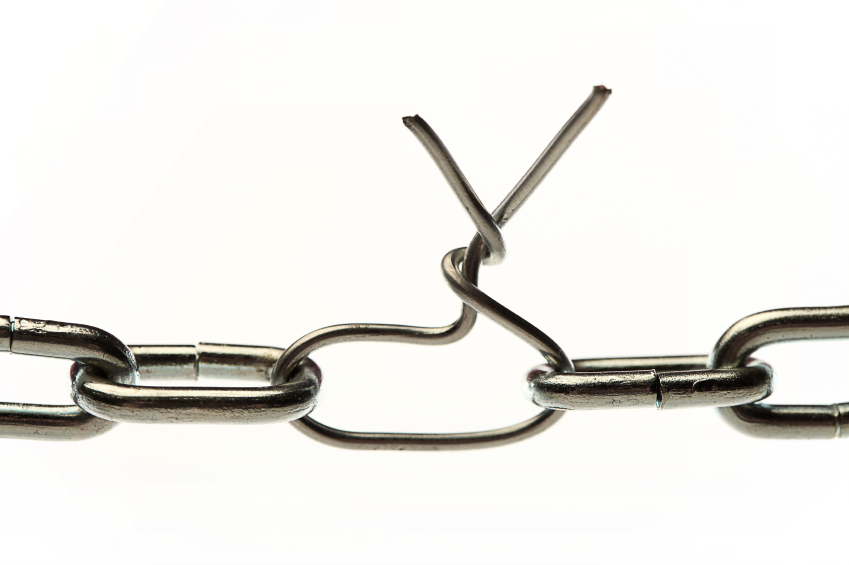
When it comes to security breaches, employees are often the weakest link in a company’s data security defense. In fact, the majority of breach investigations I’ve been involved with trace back to employee mistakes – usually inadvertent mistakes. This anecdotal evidence is also consistent with reported breaches. Consider for example, the following:
- Aetna discovered on May 28, 2010 that a file cabinet containing individual health information was not cleaned out before it was given to a vendor for removal. The documents inside the file cabinet contained the individual health information of approximately 6,372 individuals, including names, addresses, zip codes, dates of birth, and social security numbers of Aetna’s members.
- Blue Cross & Blue Shield of Rhode Island reported on April 6, 2010, that it had inadvertently donated a filing cabinet to a non-profit organization on December 20, 2009, that contained approximately 12,000 members protected health information. This information included names, addresses, telephone numbers, Social Security numbers, and Medicare identification numbers.
Again, these examples, like many others, are human and process failures – not technology failures.
Recommendations for Preventing Data Breaches
Businesses are a prime target for casual and organized hackers because they often maintain troves of consumer data. To guard against data breaches it is important to be proactive and not reactive. A few points that businesses should consider include:
- Develop, implement, and test the data breach response plan. That plan should identify a response team and tasks each member is responsible for once a breach is discovered;
- Educate and train all employees who have access to Personal Information about best practices for protecting this data while in their possession and on the appropriate use and transfer of this information. Updates on information security best practices and the latest threats should be provided on a regular basis; and
- Assess what information the business organization possesses and only retain data that serves a business or legal purpose. Properly secure the data to be retained with respect to industry acceptable standards and legal requirements. And properly dispose of information that will no longer be retained.
A complete data security protocol is beyond the scope of this post. It should, however, be developed in collaboration with internal IT professionals, executive management, and legal counsel. But a signficant cornerstone of this protocol must focus on educating and training employees on best practices for handling consumer data.